The dangers of default credentials
Default credentials are useful for logging in to systems initially, but shouldn't remain in place afterwards.
Passwords are a fact of life, whether they take the form of a simple PIN, a word or a random generated string of letters and numbers. The IT industry understands the need to protect devices so sets a username and password as the device leaves the factory - default credentials. Leaving this unchanged can be a major problem though.
Surely the password is unique to me?
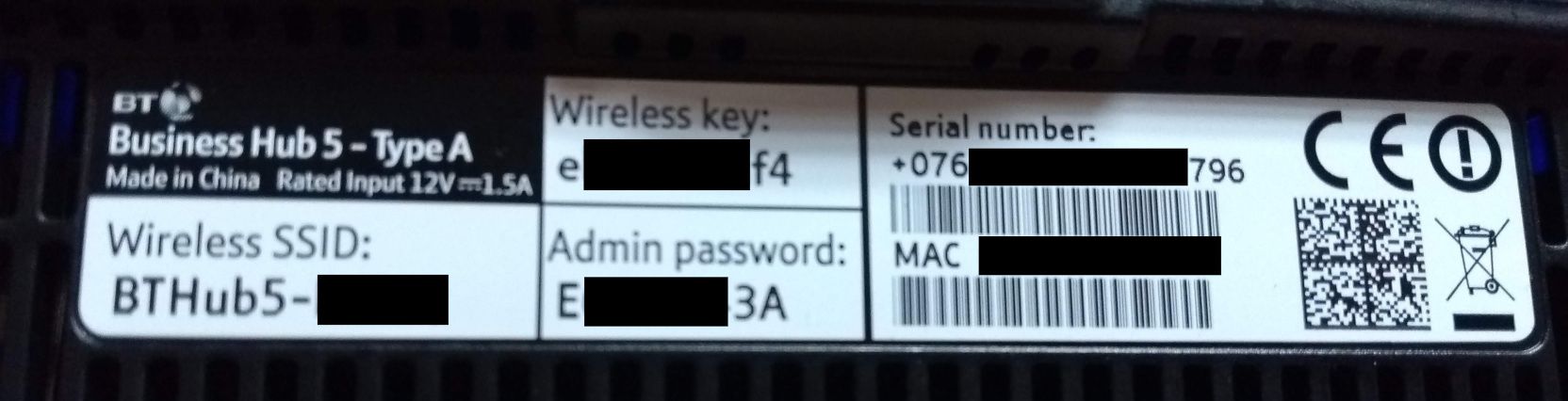
There's been movement over time to equipment coming with what looks like a random string of letters and numbers, something like ed3CWFfd83w, and that's a significant improvement over the standard "admin admin" username and password combination. Nonetheless, there's no guarantee that the random string printed on your equipment is unique to you, nor that it can't be generated with information available elsewhere. For example, an ISP in England issues their routers with a wireless network configured with names like BTHUB5-HC23. There could be a link between the WiFi password and the name. Similarly it's possible the equipment's MAC address [1] could be linked to the password generation routine - it's not clear.
The tale of the printer
As part of my job I have to keep an eye on the devices on the network and I came across a printer that could be managed via a web page. This is fairly common in modern networked printers, for example, this is mine at home:
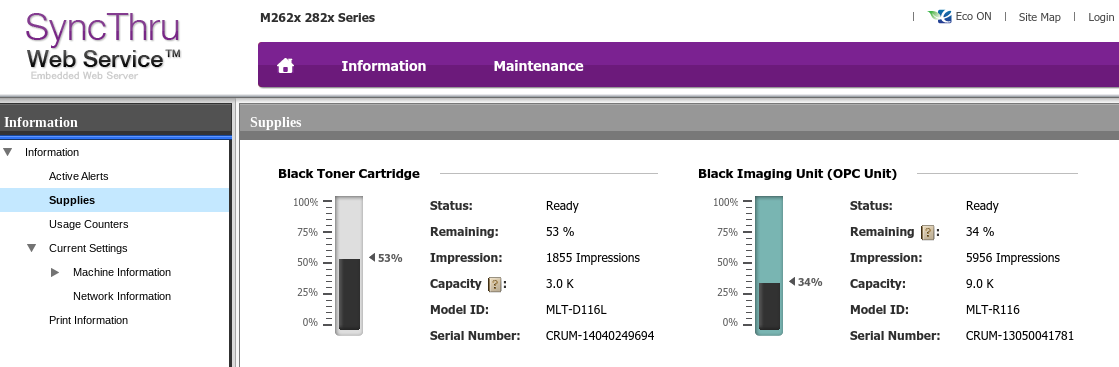
Without logging in to the printer at work I was able to see consumable usage (toner etc.) but it was the password protected area that I was particularly interested in. After logging in I found there was a full address book, used for scan to email, plus scanned or printed documents seemed to be stored for repeat usage. This posed two issues. Firstly I could change entries in the address book so that any documents got emailed to me instead and secondly I could download previous documents. As a proof of concept I downloaded a few and came across pay slips and invoices amongst other confidential documents.
For an attacker this printer would have been a potential gold mine of information. The ability to have new documents arrive at the attacker's own email address would have allowed for a level of persistence (continued access) - there's bound to be an interesting document turn up at some point! A forward thinking attacker would set a rule on their own mailbox (or a set up a distribution group) so the employee still got the scanned image and was none the wiser.
Solution: change the password.
Best solution: change the password and disable the functionality if possible.
The tale of the UPS
An organisation that I work with had a new UPS that came with a network management card put into their data centre. Sounds grand - the UPS can send alerts in the event of a problem. My requirement was that the management card had to be subjected to a vulnerability scan and this turned up two things. First - old firmware, by over a year. Quite why the supplier didn't upgrade it at point of installation I'll never know. Secondly there was a default password and after logging in to confirm the finding I was met with this:
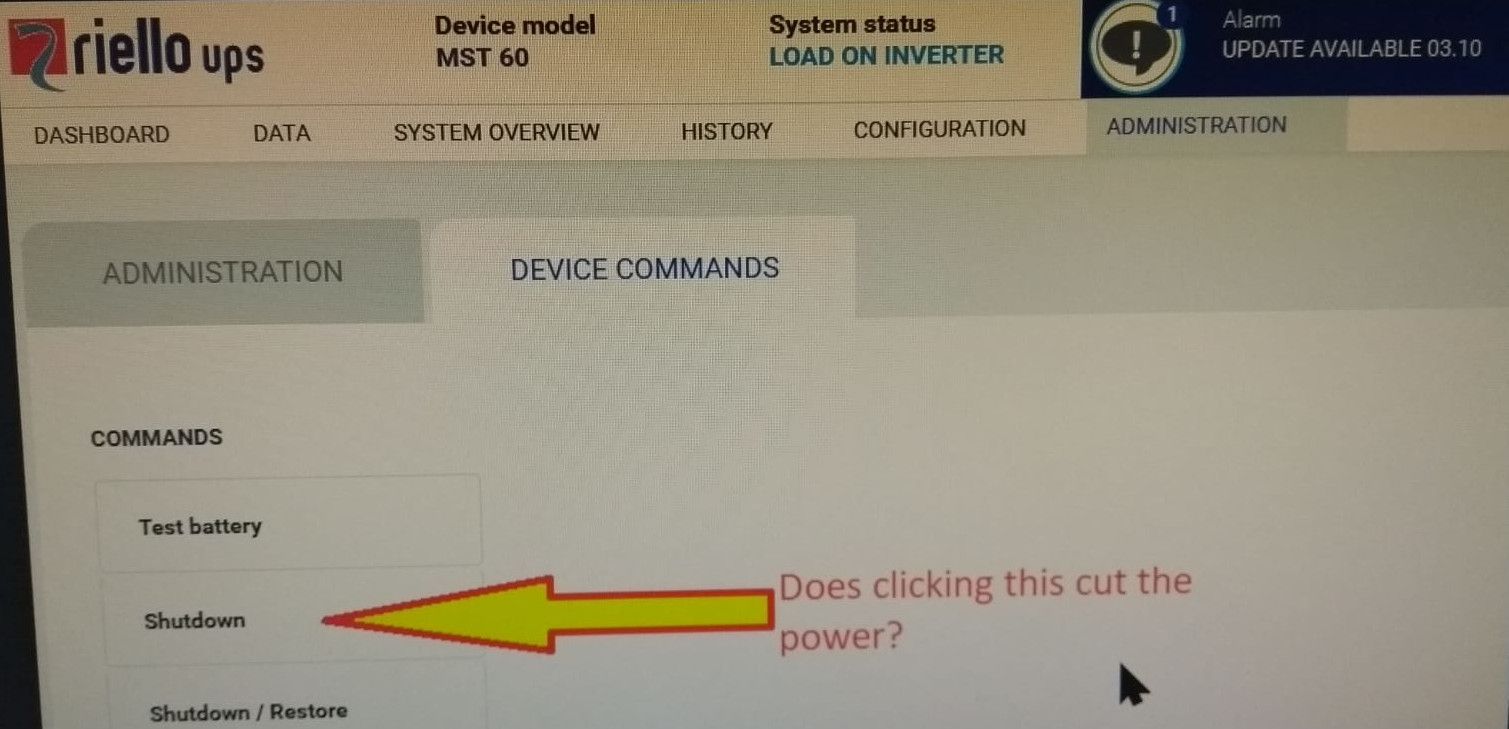
Regardless of what page of the web interface you're on you see the "update available" alert, so not upgrading that was inexcusable as far as I'm concerned. As the photo above shows there's a button for shutdown and, I assure you, the temptation to click that button was quite immense! Instead I reached for the manual and found that:
Clicking shutdown disconnects the load from the UPS.
In other words it was possible to power off the entire data centre via this poorly secured management interface. That's quite a risk and I only mention it now because I know the password has been changed (and I've confirmed that).
Solution: change the password.
Better solution: change the password and heavily restrict which parts of the network can reach the management interface.
IoT is guilty too
You'd think with IoT devices being (relatively) new, and the default password problem being well known, that this would be a solved problem on IoT equipment. Sadly not so. I recently bought a Shelly Flood Sensor and was surprised to find there was no admin password at all. I'm sure Shelly aren't the only ones guilty of this (I'm still new to IoT and home automation) and I accept that for some devices their physical size limits printing a default password onto them. If you're installing any IoT devices I strongly urge you to use caution and secure your devices appropriately.
What should you do?
Whenever you receive a device or an account, change the password unless you're unable to. Similarly, change the default password for your wifi.
If you're an organisation it's worth writing into your policies that you won't leave default credentials in place. Given that the management team has to approve policies it's useful having that requirement in place - helps to focus the minds of both employees and, hopefully, suppliers.
Finally, don't be complacent. Run audits to check for default credentials and then take corrective action when necessary.
Banner image: Photograph of some default credentials on equipment
[1] MAC address - The Media Access Control address is a unique address that's "burnt in" to the hardware and, generally, doesn't change. It's worth noting that it is possible to change what MAC address your device presents to the network, so MAC cannot be relied upon. Also worth noting that both iOS and Android have started to use virtual / variable MAC addresses to help increase privacy by stopping the MAC being used for tracking.

